Leaderboard
Popular Content
Showing content with the highest reputation on 04/12/2023 in all areas
-
2 points
Time Left: 6 months and 14 days
- FOR SALE
- NEW
NFC ATM Jackpotting Malware. Works only at NCR SelfServ NCR ProCash modes (WORLDWIDE). Withdraws all cassettes one-by-one. DOESN'T REQUIRE USB ACCESS OR ANY PHYSICAL INSIDE ACCESS. Injects through NFC card. You will need a very specific software to use it. I'll help with links where you can buy it. Overall spendings will be around 50-100 USD. I will stop selling at any time. As soon as I realize that too many people use it.. Manual and safety guide will be included with software. Any technical details won't be shared until funds are in escrow.$2,200.00
-
2 points
-
2 points
Time Left: 4 months and 25 days
- FOR SALE
- NEW
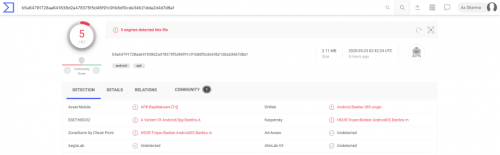
Dissecting DEFENSOR: a stealthy Android banking malware Android malware apps are nothing new, but this one is of particular interest in how it implements no such functionality that can be readily detected by security products. The apps named DEFENSOR ID and Defensor Digital rely mainly on Android's Accessibility Service to conduct malicious activities, and go undetected. In fact, a blog post released May 22nd 2020 by malware researcher Lukas Stefanko of ESET states, "the banking trojan was available on Google Play at the time of the analysis. The app is fitted with standard information-stealing capabilities; however, this banker is exceptionally insidious in that after installation it requires a single action from the victim – enable Android’s Accessibility Service – to fully unleash the app’s malicious functionality." The blog post also demonstrates at the time of its inception, no antivirus engine detected this malware sample. Even today, only 5-6 detection engines are flagging these two apps, according to VirusTotal. This raises concern for the next iteration of malware that may be nothing but a slight modification of these apps. Android Accessibility Service To make smartphones more accessible to users with special needs, the Accessibility Service allows for the device to extend permissions to an app to read screen content (e.g. for providing text to speech synthesis capability). You can imagine how useful would such a functionality be to a malicious app. Existing detection models can reliably predict when certain combinations of permissions requested by an app may pose problems. But because the Defensor apps mainly relied on obtaining Accessibility Service permissions from the user, along with some other minimalistic ones, no red flags were raised anywhere. The permissions requested by the app include the following, of which the critical ones are highlighted: android.permission.INTERNET android.permission.SYSTEM_ALERT_WINDOW android.permission.BIND_ACCESSIBILITY_SERVICE com.secure.protect.world.permission.C2D_MESSAGE android.permission.ACCESS_NETWORK_STATE android.permission.FOREGROUND_SERVICE android.permission.REQUEST_DELETE_PACKAGES android.permission.SYSTEM_OVERLAY_WINDOW android.permission.WAKE_LOCK android.permission.WRITE_SETTINGS com.google.android.c2dm.permission.RECEIVE In practice, this means the app can capture credentials entered by the user on mobile banking apps, read or generate SMS messages, read emails, read Two-Factor Authentication (2FA) codes generated by authenticator apps — thereby bypassing 2FA, steal cryptocurrency private keys, and so on, and upload all of this vital information to an attacker-controlled server! The app also requests the WAKE_LOCK permission, letting it override the default screen timeout setting, and keeping the device turned on persistently. This would give malware an extended opportunity to launch other apps and to continuously capturing sensitive information. The screenshots provided by ESET demonstrate this behaviour: Indicators of Compromise (IOCs) To make things easy for the security community, malware researchers at ESET have thankfully provided two useful IOCs identifying the malicious apps that have now been yanked from the Google Play store. Package Name SHA-1 Hash SHA-256 Hash ESET detection name com.secure.protect.world F17AEBC741957AA21CFE7C7D7BAEC0900E863F61 BBFB6DEDC01492CA3AC0C4F77343A22162518B306660E9CE958F2A6369FFAF13 Android/Spy.BanBra.A com.brazil.android.free EA069A5C96DC1DB0715923EB68192FD325F3D3CE B5A64791728AA641838D2A478375F5D46F91C91B8DF0CDE34B21DDA2D4D7D8A1 Android/Spy.BanBra.A New information and my analysis ESET researchers have done a brilliant job of presenting their comprehensive analysis of these apps and their documented behaviour. Further to their report however, I'd like to add a bit of my own findings. Command & Control (C&C) domains The attacker controlled C&C domains are still up — well at least one of them, and that's problematic. Domain IP address Task empresasenegocios.online 132.148.42.16 Command & Control (C&C) atendimentoempresarial.digital 184.168.221.46 Command & Control (C&C) The URLs specifically used by the app to establish communication between the attacker-controlled server include: https://empresasenegocios.online/remoteControl/ https://empresasenegocios.online/remoteControl/api/main/index/ http://atendimentoempresarial.digital/remoteControl/api/main/index http://atendimentoempresarial.digital/remoteControl/ Interestingly, VirusTotal reports most antivirus engines are still not flagging these URLs, except for FortiNet which flags just one of the empresasenegocios.online URLs as phishing: Nevermind the fact, the empresasenegocios.online domain still has a fancy admin panel for the attackers to log into and glance over the juicy details of their victims 🍿: Here's also a preview of the API: And the domain continues to be hosted on GoDaddy's shared hosting, with its beautiful cPanel and WebMail interfaces accessible: empresasenegocios.online/cpanel: empresasenegocios.online/webmail: At least, atendimentoempresarial.digital domain has its GoDaddy parking page showing up for now. While that's no guarantee that the domain's malicious ownership or activities have ceased, so far there are no strong signs indicating ongoing activity either. The WHOIS records of these domains didn't reveal anything particularly interesting other than Sãu Paulo, Brazil addresses and phone numbers, which could very likely be fakes, along with two email addresses belonging to the anonymous ProtonMail service: [email protected] and [email protected]. The Takeaways Enforcing BYOD policies Because prominent antivirus engines are not detecting apps like these — even now, advice to "scan your mobile device" is futile. SOC analysts and Security Ops professionals are strongly advised to enforce a corporate mobile device policy which restricts employee access to Google Play app store on their work devices. Apps like these pose significant threats to an organization's secrets especially when an organization has a relaxed Bring Your Own Device (BYOD) policy, allowing for corporate email accounts to be accessible on an employee's personal mobile device (e.g. Gmail's Android app managing both personal and work accounts of a user would not be immune to attacks like these, and could easily infiltrate corporate trade secrets to malicious actors). Network monitoring and blocks Additionally, extensive network monitoring in your SIEM/EDR products should be setup for these servers, with network blocks implemented, given at least one of these domains is still active. That way, any device on your corporate network would be prevented from inadvertently making calls to these domains. Note: The IP addresses appear to belong to GoDaddy's shared hosting, therefore blocking these could potentially block legitimate websites. It is best to block the malicious domains for the time being. DEFENSOR ID and Defensor Digital were just two of the apps which have been identified and removed from the Play store, but given their stealthy behaviour, we do not know as of yet how many other apps might be using these servers or leveraging the Accessibility Service weakness.$299.00
-
2 points
-
2 points
Time Left: 6 months and 15 days
- FOR SALE
- NEW
NATWEST SCAMPAGE .ZIP FILES UPLOAD AND UNZIP EDIT NECESSARY FILES WITH SOFTWARE OR ON SERVER UNDETECTABLE TO MANY SERVER INSTAT DELIVERY PLEASE CONTACT ME IF MORE HELP IS REQUIRED FOR ANY PRODUCT. DO NOT DISPUTE AN ORDER THE ADMIN IS VERY BUSY AND THEY WILL TAKE FOREVER TO SOLVE YOUR EMOTION ISSUES$200.00
-
2 points
Time Left: 11 months and 10 days
- FOR SALE
- NEW
The world's only wireless bluetooth magnetic stripe credit card reader writer,smallest and portable Hico and loco: all compatible (300~4000 oe); Three Tracks: track 1,2,3; Functions:read, write and erase; LED indicator, applicable and full support for ISO 7811-6 standards Bluetooth and USB interface works with Windows OS, Android, Mac OS, iPhone and iPad Download "EasyMSR" from "Google Play" or "App Store" for Android Mobile/Tablet or iPhone,iPad Using Free software for Windows and Mac OS. Paid APPs for Android and iSO(iPhone, iPad), about $20 for the EasyMSR app$300.00
-
2 points
Time Left: 11 months and 4 days
- FOR SALE
- NEW
Hello! My name is J. G. I have been carding for more than 5 years. Now I want to teach this to everyone. I guarantee that everyone will get new knowledge and a large income. Table of contents for full training: Introduction to terminology and general descriptions. Complete configuration of various systems, the latest configuration methods. Configuring dedicated server, shared security. VDS servers. Socks4/5, SSH. Configuring the virtual machine. Froude control. ABC reconciliation Buy goods in various ways at the expense of other people. We withdraw funds from payment systems. We make transfers (PayPal, Western union, Moneygram and others) Make transfers to your accounts. Search for drops Payment methods for hotels, deposits, and air travel with other people's cards. Buying, extracting information for carding. I share a list of my suppliers. Why is it worth taking the training with me? The most up-to-date information, all-wheel drive. A lot of schemes, shops, ways to cash out, work with various materials, transfers to funds, and so on. Constant support and communication after training. Joint growth, after completing your training , your development will not stop. We will share information with you constantly. (FREE) Whatever your initial level, we will bring you to profit.$499.99
-
1 point
Time Left: 6 months and 15 days
- FOR SALE
- NEW
BARCLAYS SCAMPAGE .ZIP FILES UPLOAD AND UNZIP EDIT NECESSARY FILES WITH SOFTWARE OR ON SERVER UNDETECTABLE TO MANY SERVER INSTAT DELIVERY PLEASE CONTACT ME IF MORE HELP IS REQUIRED FOR ANY PRODUCT. DO NOT DISPUTE AN ORDER THE ADMIN IS VERY BUSY AND THEY WILL TAKE FOREVER TO SOLVE YOUR EMOTION ISSUES$200.00
-
1 point
Time Left: 6 months and 15 days
- FOR SALE
- NEW
CIBC SCAMPAGE .ZIP FILES UPLOAD AND UNZIP EDIT NECESSARY FILES WITH SOFTWARE OR ON SERVER UNDETECTABLE TO MANY SERVER INSTAT DELIVERY PLEASE CONTACT ME IF MORE HELP IS REQUIRED FOR ANY PRODUCT. DO NOT DISPUTE AN ORDER THE ADMIN IS VERY BUSY AND THEY WILL TAKE FOREVER TO SOLVE YOUR EMOTION ISSUES$200.00
-
1 point
Time Left: 1 month and 13 days
- FOR SALE
- NEW
Hello everybody! Welcome to my WOLOW MONEY TRANSFER service. Paypal is one of the destinations. The minimum transfer amount is 1000$ 1000$ - 400$ (my share) 2000$ -700$ (my share) 3000$ - 900$ (my share) 4000$ - 1000$ (my share) 5000$ -1200$ (my share) https://t.me/wolowmoneytransfer$400.00
-
1 point
Time Left: 11 months and 5 days
- FOR SALE
- NEW
To infect the device, it is enough for the user to click on the link or open the image. Up to $ 1000 per year with 1 connected device. The number of connected devices depends on you, there may be 10 or even 10,000. Antivirus programs do not react to infection in any way. Additional questions in telegram or PM$999.00
-
1 point
Time Left: 11 months and 4 days
- FOR SALE
- NEW
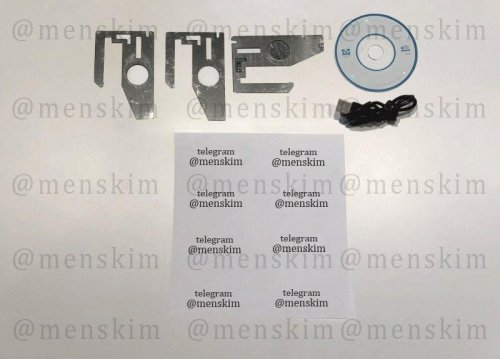
Ncr, Wincor Nixdor, Diebold Insert Skimmer.Full Kit ready for work.Battery can last up to 48 hours,outside temperature doesn’t affect to skimmer working time, because skimmer is located inside ATM.Store up to 15000 credit card tracks. Full Kit Include Insert and remove tools, data cable,software CD, this is plug and play product that is ready for work. Available to order PIN pad as extra option.$1,000.00
-
1 point
Time Left: 11 months and 4 days
- FOR SALE
- NEW
NEW VERSION AVAILABLE – NEW INTERFACE, UPGADED ANTENNA, MODEL V22.3.4 LTE2017-2018 year model. ATM Skimming without any physical contact. This Skimmer will work without a physical connection to ATM/POS Machine. This product is our best-seller, and is most popular credit card skimming device Worldwide. This is GSM data receiver – skimmer. It receives credit card data from ATM`s and POS terminals. Small size 5×4 Centimeters, antenna length 17 centimeters. With one charging it can work up to 8 hours and the manufactured memory can capture about 100000 credit card data, with antenna it can take data in radius of 50 meters. Device can work from (-25 to +45 degrees). We use 3.7V 2500mAh batteries. With one charging the device can work up to 8-10 hours. It have built in a built in memory 32 gb, it can store up to 100000 credit card details with pin codes. Briefly – GSM data receiver is a GSM module receiver which with the help of special software clones and receives all credit card information from ATM`s and POS terminals. The received information is stored by your phone or laptop. To collect this information, you just need to connect the device to your computer or mobile device and the device will send the data to your computer, with the help of the software V22.3.4. GSM receiver have also implemented a new feature, option to add power bank to incase skimming lifetime. GSM data receiver is small & you can easily hide it in your bag, clothes, pocket, or in your car – near the POS/ATM terminal. Device has two led lights – Red and Green Red – Device needs to charge. Flashing red – Device can work for 30 – 40 min more, afterwards it needs to be recharged or added power bank or usb charger. Green+Red – Device is working. Flashing green – Device is connecting. Price for GSM Data Receiver $1000 USD with shipping included. Price for GSM Data Receiver + MSR encoder and 100 pcs cards $1215USD with shipping included.$1,000.00
-
1 point
-
1 pointthanks for posting mate much appreciated
-
1 point
-
1 point
-
1 point
-
1 pointGuys it took time to crack those accounts so please leave a like if you enjoyed, it will help me to post more accounts LIKE FOR MORE BUNCH OF ACCOUNTS! Every Leecher will get reported and banned Accounts: [hide] https://pastr.io/view/WT12Xh [/hide]
-
1 point
-
1 pointThis is HQ af! great share
-
1 pointgreat job thanks for share
-
1 pointLove the british girls. thanks for getting this out there man
-
1 point
-
1 point
-
1 point
-
1 point
-
1 pointYasssssssssssssss Yo this a bump
-
1 point
-
1 point
-
1 point
-
1 point
-
1 point
-
1 point
-
1 point
-
1 point
-
1 point
-
1 point
-
1 point
-
1 pointPro leaker thank you :fiesta:
-
1 point
-
1 point
-
1 point
-
1 point
-
1 point
-
1 point
-
1 point
-
1 point
-
1 point
-
1 pointthanks for sharing. like, if i got hits :-)








.thumb.jpg.53e4796db1714ce82c347c7e7ab13da1.jpg)