DEFENSOR ID a stealthy Android banking Trojan - Source Code
DEFENSOR ID a stealthy Android banking Trojan - Source Code
$299.00
-
Advertiser
- Type of Advert FOR SALE
- Item Condition NEW
- Time Left 1 month and 30 days -
- Quantity 1
- Price $299.00
- 1 watching
Description
Dissecting DEFENSOR: a stealthy Android banking malware
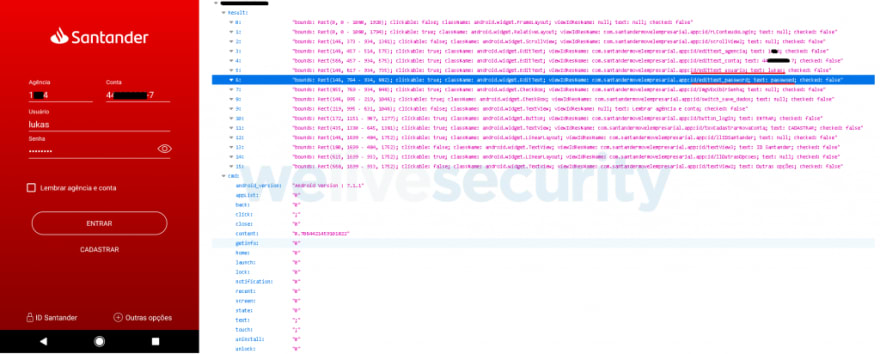
Android malware apps are nothing new, but this one is of particular interest in how it implements no such functionality that can be readily detected by security products. The apps named DEFENSOR ID and Defensor Digital rely mainly on Android's Accessibility Service to conduct malicious activities, and go undetected.
In fact, a blog post released May 22nd 2020 by malware researcher Lukas Stefanko of ESET states, "the banking trojan was available on Google Play at the time of the analysis. The app is fitted with standard information-stealing capabilities; however, this banker is exceptionally insidious in that after installation it requires a single action from the victim – enable Android’s Accessibility Service – to fully unleash the app’s malicious functionality."
The blog post also demonstrates at the time of its inception, no antivirus engine detected this malware sample.
Even today, only 5-6 detection engines are flagging these two apps, according to VirusTotal. This raises concern for the next iteration of malware that may be nothing but a slight modification of these apps.
Android Accessibility Service
To make smartphones more accessible to users with special needs, the Accessibility Service allows for the device to extend permissions to an app to read screen content (e.g. for providing text to speech synthesis capability). You can imagine how useful would such a functionality be to a malicious app.
Existing detection models can reliably predict when certain combinations of permissions requested by an app may pose problems. But because the Defensor apps mainly relied on obtaining Accessibility Service permissions from the user, along with some other minimalistic ones, no red flags were raised anywhere. The permissions requested by the app include the following, of which the critical ones are highlighted:
- android.permission.INTERNET
- android.permission.SYSTEM_ALERT_WINDOW
- android.permission.BIND_ACCESSIBILITY_SERVICE
- com.secure.protect.world.permission.C2D_MESSAGE
- android.permission.ACCESS_NETWORK_STATE
- android.permission.FOREGROUND_SERVICE
- android.permission.REQUEST_DELETE_PACKAGES
- android.permission.SYSTEM_OVERLAY_WINDOW
- android.permission.WAKE_LOCK
- android.permission.WRITE_SETTINGS
- com.google.android.c2dm.permission.RECEIVE
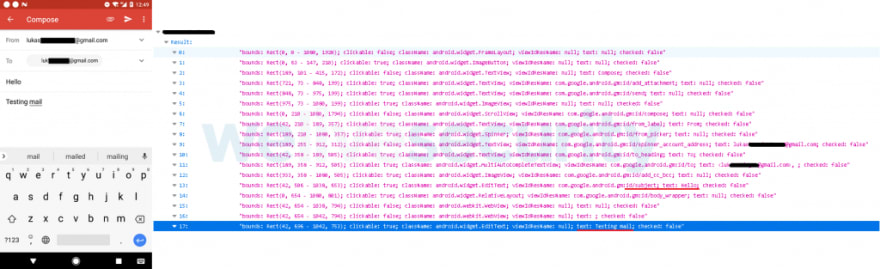
In practice, this means the app can capture credentials entered by the user on mobile banking apps, read or generate SMS messages, read emails, read Two-Factor Authentication (2FA) codes generated by authenticator apps — thereby bypassing 2FA, steal cryptocurrency private keys, and so on, and upload all of this vital information to an attacker-controlled server!
The app also requests the WAKE_LOCK permission, letting it override the default screen timeout setting, and keeping the device turned on persistently. This would give malware an extended opportunity to launch other apps and to continuously capturing sensitive information.
The screenshots provided by ESET demonstrate this behaviour:
Indicators of Compromise (IOCs)
To make things easy for the security community, malware researchers at ESET have thankfully provided two useful IOCs identifying the malicious apps that have now been yanked from the Google Play store.
| Package Name | SHA-1 Hash | SHA-256 Hash | ESET detection name |
|---|---|---|---|
| com.secure.protect.world | F17AEBC741957AA21CFE7C7D7BAEC0900E863F61 | BBFB6DEDC01492CA3AC0C4F77343A22162518B306660E9CE958F2A6369FFAF13 | Android/Spy.BanBra.A |
| com.brazil.android.free | EA069A5C96DC1DB0715923EB68192FD325F3D3CE | B5A64791728AA641838D2A478375F5D46F91C91B8DF0CDE34B21DDA2D4D7D8A1 | Android/Spy.BanBra.A |
New information and my analysis
ESET researchers have done a brilliant job of presenting their comprehensive analysis of these apps and their documented behaviour. Further to their report however, I'd like to add a bit of my own findings.
Command & Control (C&C) domains
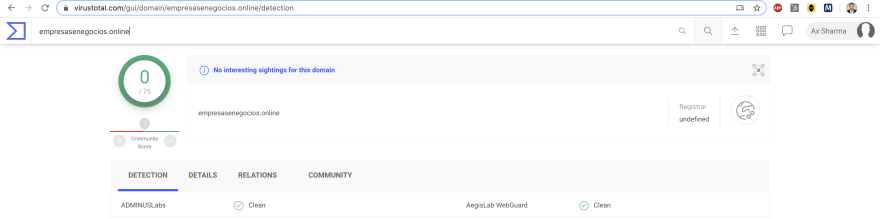
The attacker controlled C&C domains are still up — well at least one of them, and that's problematic.
| Domain | IP address | Task |
|---|---|---|
| empresasenegocios.online | 132.148.42.16 | Command & Control (C&C) |
| atendimentoempresarial.digital | 184.168.221.46 | Command & Control (C&C) |
The URLs specifically used by the app to establish communication between the attacker-controlled server include:https://empresasenegocios.online/remoteControl/https://empresasenegocios.online/remoteControl/api/main/index/http://atendimentoempresarial.digital/remoteControl/api/main/indexhttp://atendimentoempresarial.digital/remoteControl/
Interestingly, VirusTotal reports most antivirus engines are still not flagging these URLs, except for FortiNet which flags just one of the empresasenegocios.online URLs as phishing:
Nevermind the fact, the empresasenegocios.online domain still has a fancy admin panel for the attackers to log into and glance over the juicy details of their victims 🍿:
Here's also a preview of the API:
And the domain continues to be hosted on GoDaddy's shared hosting, with its beautiful cPanel and WebMail interfaces accessible:
empresasenegocios.online/cpanel: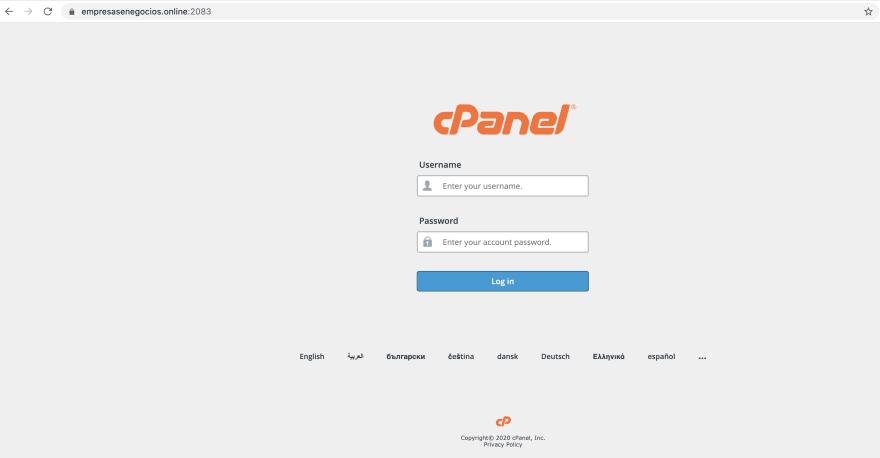
empresasenegocios.online/webmail:
At least, atendimentoempresarial.digital domain has its GoDaddy parking page showing up for now. While that's no guarantee that the domain's malicious ownership or activities have ceased, so far there are no strong signs indicating ongoing activity either.
The WHOIS records of these domains didn't reveal anything particularly interesting other than Sãu Paulo, Brazil addresses and phone numbers, which could very likely be fakes, along with two email addresses belonging to the anonymous ProtonMail service: [email protected] and [email protected].
The Takeaways
Enforcing BYOD policies
Because prominent antivirus engines are not detecting apps like these — even now, advice to "scan your mobile device" is futile.
SOC analysts and Security Ops professionals are strongly advised to enforce a corporate mobile device policy which restricts employee access to Google Play app store on their work devices.
Apps like these pose significant threats to an organization's secrets especially when an organization has a relaxed Bring Your Own Device (BYOD) policy, allowing for corporate email accounts to be accessible on an employee's personal mobile device (e.g. Gmail's Android app managing both personal and work accounts of a user would not be immune to attacks like these, and could easily infiltrate corporate trade secrets to malicious actors).
Network monitoring and blocks
Additionally, extensive network monitoring in your SIEM/EDR products should be setup for these servers, with network blocks implemented, given at least one of these domains is still active. That way, any device on your corporate network would be prevented from inadvertently making calls to these domains.
Note: The IP addresses appear to belong to GoDaddy's shared hosting, therefore blocking these could potentially block legitimate websites. It is best to block the malicious domains for the time being.
DEFENSOR ID and Defensor Digital were just two of the apps which have been identified and removed from the Play store, but given their stealthy behaviour, we do not know as of yet how many other apps might be using these servers or leveraging the Accessibility Service weakness.
-
 386
386












.thumb.jpg.53e4796db1714ce82c347c7e7ab13da1.jpg)





.thumb.jpg.fefac019f1222e64407746f16d30e464.jpg)

